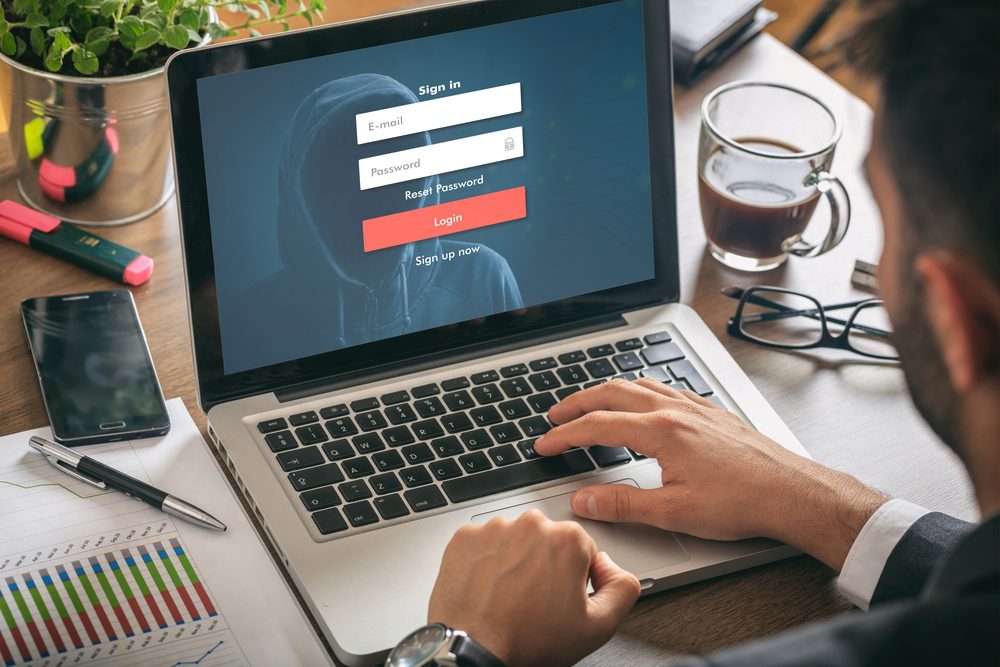
If you’ve spent enough time on the internet up until now, you’ve probably been in contact with a phishing attempt. Phishing is a cybercrime in which the target is contacted via e-mail by a hacking system that pretends to be a legitimate institution.
The purpose of this is to lure individuals in giving their personal data, such as banking and card information, or passwords. This way, the hacker manages to steal your data, uses it to enter personal accounts and steal your money or your identity.
The first phishing lawsuit dates back to 2014 against a Californian teenager. He managed to create an imitation of the website “America Online” where he stole private information from its users to access their credit cards. But this is not the only famous example of phishing.
One of the most significant cyberattacks happened in 2016 when a group of Russian hackers set their target on Clinton’s campaign chairman John Podesta. He received an e-mail from a suspicious source that warned him someone has his password and that he needed to change it immediately.
Even Clinton campaign’s own computer help desk believed the e-mail was sent from Google, although the link had a suspicious “googlemail.com” extension.
These phishing methods are specifically tailored for human curiosity and wish for luck. Let’s see how you can recognize and avoid them while surfing on the internet.
How to recognize phishing emails
Hackers have developed over time a fantastic ability to disguise phishing attacks in normal emails. The truth is, with the help of technology, they are getting better everyday. Let’s see some common items we can recognize when running into a phishing attempt:
Dreamy promises- be careful of eye-catching or attention-grabbing offers! Statements as “You’ve just won your first iPhone! Claim it now !” or “You’ve won the big prize!” are made to lure you into believing you’ve won something lavish when in reality it’s only a scam.
If something similar ever appears in your email, don’t ever click it. If it seems too good to be true…it most likely is!
- Hasty voice- A practiced cyber scam is to urge you to press the button that will help hackers access your data. Messages such as “You’ve only got 5 minutes to claim your prize now” or “Hurry up! Your account might get suspended now” are common tricks used to hack your computer. If you see anything like that, just ignore it. Usually, legitimate organizations give you enough time to update your account and will never pressure you in this kind of situation. If you have doubts, just go to the original source and check with your data.
- Hyperlinks- You should always check the link that is given to you in these e-mails. Hackers have multiple methods of faking a source, but you can always check it before deciding to click on it.
- Attachments- Another common method of phishing via e-mail is attaching a suspicious attachment. If you haven’t been expecting one, don’t click on it. For extra safety, remember that the safest attachments are usually the ones that have a .txt format. Other than that, ignore them.
- Unusual sender- If it doesn’t seem familiar to you, you should definitely don’t click it. This is advice that you need to listen to: trust your instinct.
Now that we wrapped up some phishing methods, let’s see what can you do to avoid them.
Learn how a phishing attack might look like
The keyword for all our advice is: update. You need to get updated on the latest cyberattacks that are out there. As technology evolves so rapidly, attackers find various methods to scam the users. You need to learn what to look for in these messages, how to recognize them and how to avoid them.
To do that, different websites can inform you of the latest cyberattacks methods and their key identifiers. It is highly recommended to learn as soon as possible about the latest updates on these attacks. The sooner you know what to look after, the better you can avoid them and sustain a better security awareness for you and your network.
Don’t click
Even if you know the sender of the e-mail, it is advisable not to click on the link. As hackers nowadays manage to create a carbon copy of an original site, it is for the best to check it by going directly to the site through a search engine.
As an alternative, if you receive an e-mail that has the slightest suspicious look, try hovering over it a little and check if the destination is the correct one. This is a safe approach that can assure you no hacker will manage to access your private information. Better safe than sorry!
Try free anti-phishing adds-on
The good aspect of evolving technology is that not only the bad guys get better by day, but also the good guys. There are plenty of browsers that will recommend you to download adds-on to help you identify phishing sites.
They are free and easy to download, so there is no reason not to try them for your safety. We want to recommend to you some of the best malware software we know, but you should keep in mind they do more than just protect you from malicious websites:
- Norton 360
- Avast (recommended for small businesses)
- Kaspersky
- Bitdefender
- Malwarebytes (recommended for Windows)
- Webroot (recommended for Mac)

Avoid giving information to unsecured sites
Another important item to look after in your e-mails is unsecured sites. You might receive an e-mail that urges you to click on a link that might turn into a phishing attack. To be always prepared, we give you some tips on how to look after a malicious link:
- Look for the “S” in “HTTPS” – this shows that the link is encrypted. This kind of security is given by an SSL Certificate, meant to protect private information when it travels from a site to a server.
- Website Privacy Policy- any website privacy policy should inform you on how your data is being collected and protected by the website.
- Find contact information- to prove its safeness, a website should always have displayed a phone number, e-mail address or any other contact information.
- Trust seal- you should always look for a trust seal when entering a website. Signs like “Secure” or “Verified” will show you that the site works with a security partner.
Change passwords regularly
Although it might seem a bit like a headache, it might be a good idea to change your passwords regularly. This advice is for the best when your account has been hacked and you don’t know it. Rather than allowing cyberbullies to access your card info or bank account, it’s better to be safe and make a habit out of changing your password from time to time.
It is highly recommended to choose a different password for all of your accounts and regularly rotate them. Like this, you keep your personal data away from any cyber threat and rest assured your accounts are safe.
Don’t ignore updates
Do you constantly receive update requests from your malware software? You believe them to be extremely annoying and usually ignore them as long as you can? You should stop doing that. Even though we might not fully understand the need of updating these programs, they prove to be helpful when it comes to phishing.
These security updates come as a solution for any modern cyber-attacking method. They patch any holes in your security system and help to avoid any phishing attacks.
But you should keep in mind there could also be fake software updates! And those are, as you imagined, phishing attempts. So just to be completely sure, you should only trust the updates given by your security software!
Avoid pop-ups
Speaking of annoying, there is nothing that gets on our nerves other than pop-ups. Besides the fact they are highly irritating, they are also very dangerous. Luckily, you can now download for free different ad-blocker software that will block any malicious pop-up that could harm your computer and have access to your data.
There are also situations where the viruses manage on infiltrating the ad-blocker security system. When this happens, we recommend you not to click it. You can identify these pop-ups by making the difference between a “Close” button and an “X” button. The “close” button will mostly mean it’s a virus, while the “x” button is safer to press.
Don’t give up important information unless it’s safe
Let’s picture this: you need to buy a gift for someone you love. You know they want a specific item, that can only be found on a suspicious source. In these situations, it’s best to make sure multiple times before giving away your card information. Besides checking for contact information, as we mentioned before, it is for the best to assure it’s not a threat.
Before completing the purchase, make sure you verify that the website is genuine, the company you want to buy from is safe and the site is secured. Instead of purchasing the item you wish, you might end up with all your money stolen, so it’s best to prevent it before it happens.
Have a data security platform
Sometimes, no matter how cautious you are with your online traffic, a virus manages to slide into your security system. When this happens, you must know what can be done next. The best aspect you should keep in mind is that time is very important, that’s why you should be able to detect and react fast.
With the help of a data security platform, it will be much easier to detect a phishing attempt. This platform will automatically alert you when it discovers suspicious user behavior or any unwanted changes to your files. Like this, you can know when you’ve been hacked and resolve the problem right away!
Check your online accounts
We don’t mean to scare you, but if you haven’t been using an online account for a while, you should check it. Nowadays, a lot of websites demand we make an account to log in, so it’s easy to forget about one if you don’t need it anymore. But if you haven’t been using it for a long time, it is possible for someone else to have.
That is why it’s for the best to ask for monthly statements from time to time, and check every entry on that account. This way, you’ll keep an eye on any possibility of fraudulent transactions that you might have not approved or be aware of.
If you enjoyed reading this article, we also recommend you:
- Wealth-building Tips From Millionaires That Work for Everyone
- These Classic Cons Have Transformed Into Online Scams Worth Millions of Dollars!








4 Responses
I simply could not go away your web site before suggesting that I extremely loved the standard info a person provide for your visitors? Is going to be again ceaselessly to investigate cross-check new posts.
I simply couldn’t go away your website before suggesting that I extremely loved the standard info an individual supply to your guests? Is going to be back ceaselessly to check up on new posts.
Hello there! I just want to give you a huge thumbs up
for the great information you’ve got right here on this post.
I will be returning to your site for more soon.
I don’t even know how I ended up here, but I thought this post was good.
I do not know who you are but definitely you are going to a famous blogger if you aren’t already 😉 Cheers!